Is Decentralized Swap Safe? 2026 Safety Guide
Quick answer: safe, but only under the right conditions
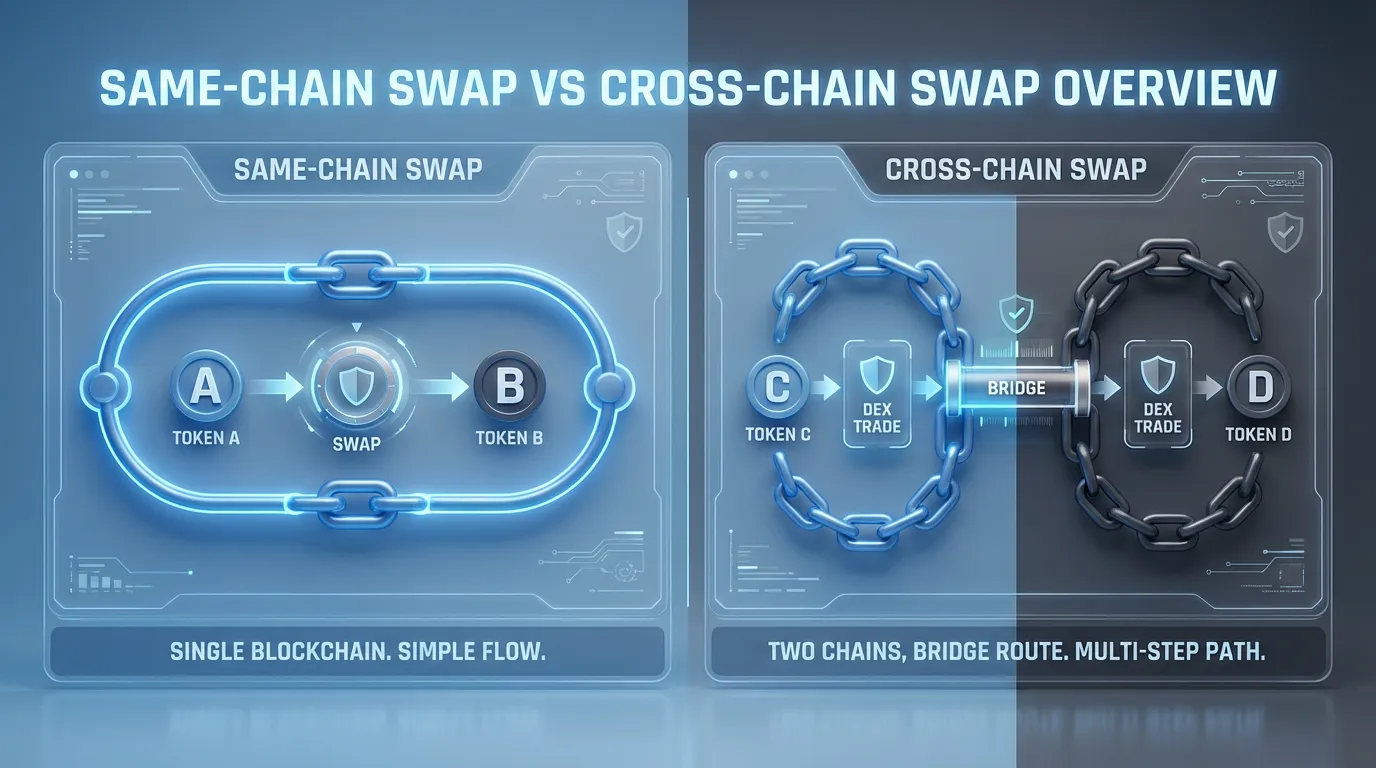
If you are asking "is decentralized swap safe" in 2026, the most accurate answer is: it can be reasonably safe for many users on mature same-chain DEX routes, but safety drops as complexity rises, especially for cross-chain swaps. The difference is not just the DEX. It is also the bridge or router design, the wallet you use, and whether you notice red flags before signing.
What a decentralized swap really does (and what it does not do)
A decentralized swap is a token-to-token trade executed by smart contracts on-chain, typically via an AMM (liquidity pools) or an aggregator that routes across venues. Unlike a centralized exchange, the DEX does not take custody the way a custodial platform does, because the swap settles directly to your address.
However, "non-custodial" does not mean "risk-free". Your risks shift from exchange insolvency to: contract bugs, malicious tokens, MEV, approvals abuse, and (if you go cross-chain) bridge and message-passing risks.
If you want deeper background on AMMs and DEX mechanics, Uniswap and Curve documentation are good starting points: Uniswap documentation and Curve documentation.
Same-chain swap safety: mature, but still attackable
Same-chain swaps have improved a lot by 2026, but the main failure modes remain consistent across incident reports and security write-ups:
- Smart contract exploits: Logic flaws can drain pools or allow unintended behavior. Chainalysis reported DeFi protocols drove a large share of stolen funds during major exploit waves (for example, in early 2022). See Chainalysis on DeFi hacks.
- MEV and sandwich attacks: Attackers can reorder transactions to extract value, especially when you set high slippage. For a practical MEV overview, see Arkham's MEV guide. Data reporting also suggests sandwich extraction on Ethereum declined substantially by 2025, helped by protection tooling: TradingView summary of EigenPhi data.
- Rug pulls and malicious tokens: Tokens can be engineered to block selling or enable privileged minting. Chainalysis has repeatedly highlighted fraud and safety concerns in DeFi activity: Chainalysis Web3 report preview.
- Phishing and UI scams: Many losses come from users signing the wrong transaction or using fake frontends, not from the DEX itself. For example, 2025 incident summaries emphasize phishing and social engineering as persistent drivers: DeepStrike 2025 losses and trends.
Same-chain vs cross-chain risk snapshot (practical view)
| Category | Same-chain swap | Cross-chain swap |
|---|---|---|
| Moving parts | One chain, one execution environment | Multiple chains, plus bridge/router and messaging |
| Typical failure | Slippage, MEV, malicious tokens, approvals | All same-chain risks plus bridge/validator/message risks |
| Recovery odds | Sometimes possible via reversals? Usually not | Usually not, plus assets can end up wrapped on another chain |
| Best beginner path | Start here on mature pairs | Use only when you truly need the destination chain |
Cross-chain swaps: why the risk is structurally higher
Cross-chain swaps add interoperability infrastructure on top of swapping. Historically, that layer has been one of the most exploited surfaces in crypto.
Chainalysis reported that in 2022, bridge hacks accounted for roughly $2B out of $3.8B stolen from crypto protocols, about two-thirds of DeFi losses that year: Chainalysis on bridge hacks as a top security risk and Chainalysis 2022 hacking overview.
From 2023 to 2025, large losses continued across DeFi, with 2025 DeFi breaches exceeding $3.1B in some aggregations: CyberDaily 2025 DeFi breaches and De.Fi Rekt Report Q3 2025.
Common cross-chain swap risks you should assume are possible
Cross-chain swap risks tend to cluster into a few repeatable buckets:
- Bridge smart contract bugs: A single verification flaw can allow minting without collateral.
- Validator or relayer compromise: Federated bridges can fail if enough keys are stolen.
- Message-passing errors: Replay protection and sequencing bugs can become catastrophic.
- Liquidity fragmentation and mispricing: Thin routes can cause worse fills and failed exits.
- Operational mistakes: Wrong destination chain, wrong asset type (native vs wrapped), or misunderstanding where the funds will land.
For a helpful conceptual overview of bridge types and tradeoffs, see: Chainalysis introduction to cross-chain bridges and LogRocket bridge guide.
Wallet comparison: what actually changes your safety outcomes
Because most people swap through a wallet UI (not raw contract calls), the wallet becomes a real safety layer. Below is a comparison focused on swap safety behaviors, not brand claims.
| Safety dimension | FoxWallet | Typical non-custodial competitors (generalized) |
|---|---|---|
| Custody model | Non-custodial, user controls keys | Non-custodial, user controls keys |
| Key storage approach | Locally encrypted mnemonic/private keys, secure sandbox isolation | Varies by implementation |
| Cross-chain UX | Built with multi-chain and cross-chain flows as first-class concepts | Often added over time; UX differs by product |
| Swap execution | Built-in multi-chain swap aggregators, routing to reduce slippage and hidden costs | Often includes in-app swaps, sometimes relies on third-party routes |
| Risk reduction | Pre-transaction risk alerts, smart contract recognition, phishing/malicious contract protection | Risk warnings vary; often depends on integrations |
What this means in practice:
- If you primarily do same-chain swaps, your biggest wins come from better transaction clarity (approvals, slippage, contract recognition) and not getting phished.
- If you do cross-chain swaps, UX and guardrails matter more, because user mistakes and bridge selection errors become common failure points.

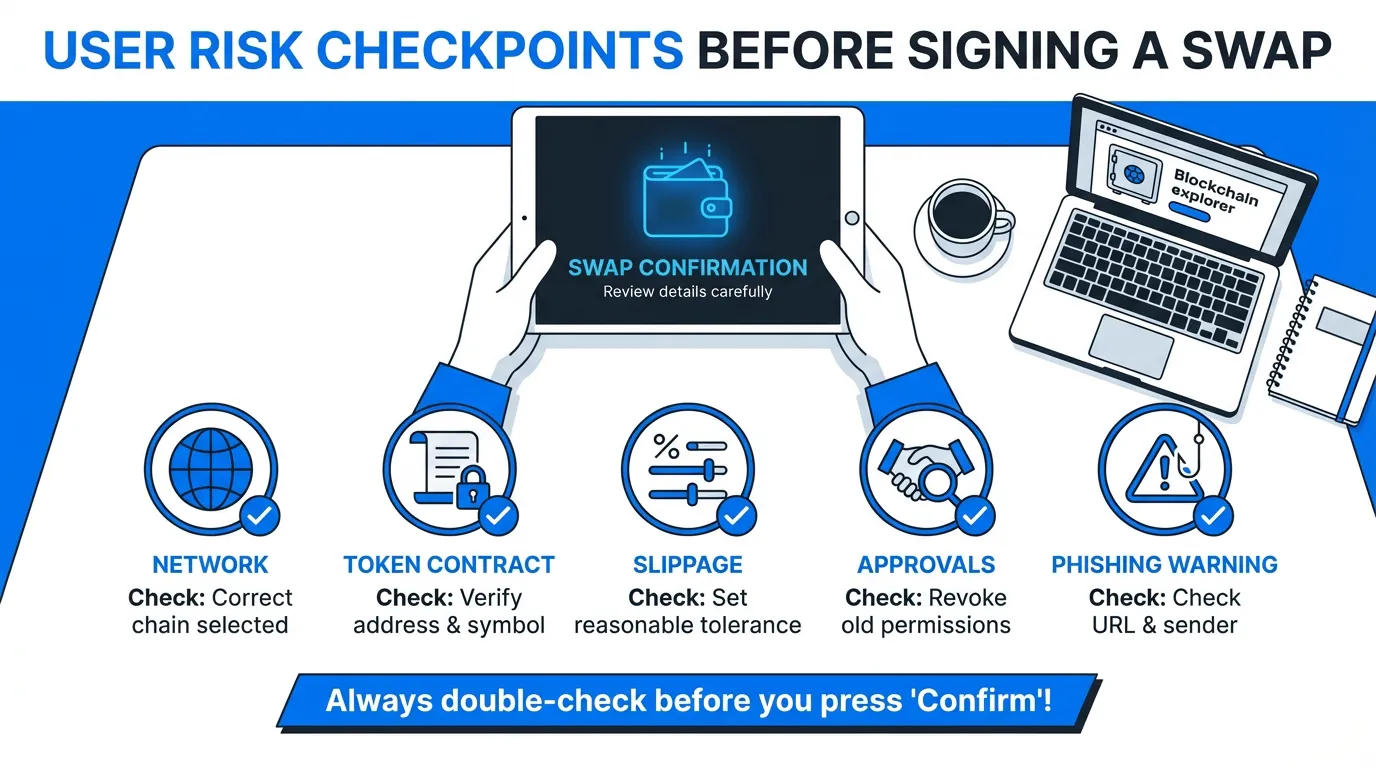
2026 safety checklist (same-chain first, cross-chain with extra discipline)
Use this as a repeatable routine before every swap:
Same-chain checklist
- Use mature protocols and liquid pairs. Low liquidity amplifies slippage and manipulation.
- Set conservative slippage. High slippage makes you a more profitable MEV target.
- Treat token approvals as a real permission. Avoid unlimited approvals when you can.
- Read the wallet warnings. If the wallet flags a contract or approval as risky and you cannot explain why, do not sign.
Cross-chain checklist
- Assume the bridge/router is the weakest link. This is consistent with Chainalysis' historical loss breakdowns.
- Do a small test swap first. Confirm the destination chain and received asset match expectations.
- Verify you understand the "final state": which chain, which token contract, and whether it is wrapped.
- Prefer wallet-integrated routing over random links. Avoid clicking bridge URLs from social posts.
Using FoxWallet as a safer swap entry point
If your goal is to reduce real-world swap risk (not chase perfect theoretical security), the practical advantages of FoxWallet map directly to common failure modes:
- Non-custodial design with locally encrypted keys means you keep control of funds.
- Multi-chain asset management and unified views reduce "where did my tokens go?" confusion after complex swaps.
- Built-in cross-chain swap aggregators reduce manual steps (and therefore reduce opportunities for errors).
- Pre-transaction risk alerts and contract recognition help you catch suspicious approvals and unknown contracts before signing.
If you want to make decentralized swaps part of your routine in 2026, start with same-chain swaps, build your habits, then move to cross-chain only when you truly need it, using a security-first wallet interface. Install and explore FoxWallet to manage multi-chain assets and approach swaps with clearer risk context.
